As COVID-19 fears grow, hundreds of Coronavirus-themed domains are being used to spread malware and steal information
Amongst growing fears of this global pandemic, Coronavirus scams and malicious websites are on the rise. The latest news from the Health Sector Cyber-security Coordination Center (HC3), a new malicious website is circulating on the internet that targets unsuspecting users.
True to their selfish nature, cyber-criminals are taking advantage of public panic about the global Corona-virus pandemic for their own selfish goals. Now, of course, this concept is nothing new. Cyber-criminals are always looking for the next best thing to take advantage of. But that doesn’t mean that it isn’t a serious issue that you can simply ignore.
So, what is this new phishing website and why should you be concerned about it? And what are some of the other Corona-virus scam tactics that cyber-criminals are using to take advantage of the global pandemic?
Let’s hash it out.
Cyber-criminals Create Corona-virus Tracker Map to Spread Info-Stealing Malware
When something’s wrong, people frequently turn to the internet to get the latest information. Cyber-criminals know this and are creating fraudulent websites that impersonate real, reputable authorities. Their latest tactic? Live tracker websites.
In truly low-life fashion, some schmuck decided to create a phishing website, corona-virus-map[dot]com (and, no, please don’t type that into your browser), that appears to be a legitimate COVID-19 live tracking map for the virus. In this case, HC3 reports that the cyber-criminals were impersonating John’s Hopkins University, a world-renowned health institution, to infect website visitors with the AZORult trojan. This program exfiltrates a wealth of sensitive data that can be sold on the dark web or used to commit cybercrimes, including cryptocurrency theft.
Here’s a screenshot from the official HC3 notification about the phishing scam site:

In general, Corona-virus themed cyber attacks and phishing websites are becoming a lot more common as news about the virus continuously blasts from virtually every media outlet. Check Point, a cyber-security firm, recently reported on their blog that CNN alone hosts more than 1,200 articles.
According to the same blog post:
“Since January 2020, based on Check Point Threat Intelligence, there have been over 4,000 corona-virus related domains registered globally. Out of these websites, 3% were found to be malicious and an additional 5% are suspicious. Corona-virus related domains are 50% more likely to be malicious than other domains registered at the same period, and also higher than recent seasonal themes such as Valentine’s day.”
In addition to users finding the website organically through web searches, the website was circulated via a variety of other tactics, including:
- malicious links and attachments in emails
- social engineering, and
- online advertising.
This newly discovered threat follows on the heels of other cyber scams, including other Coronavirus-themed malware and phishing emails.
Coronavirus-Themed Phishing Emails Are on the Rise
Another way that cyber-criminals are taking advantage of a bad situation is by launching Coronavirus-themed email phishing campaigns. In a February notification, the HC3 reported that carefully crafted phishing emails are sent to entice users to open attachments or to click on links that contain malware that’s frequently used to target healthcare organizations and their IT systems.
According to the HC3:
“Victims who interact with malicious links or attachments may expose their systems, networks, and valuable information. These exposures allow an attacker to use infected systems as a platform to launch additional attacks.”
In these campaigns, cybercriminals impersonate a variety of organizations, including the U.S. Centers for Disease Control and Prevention (CDC), the World Health Organization (WHO), and a Japanese disability welfare service provider. But Coronavirus scams don’t stop where the digital world ends — criminals are impersonating federal authorities in face-to-face scams as well.
According to Check Point, one particularly widespread phishing campaign targeted more than 10% of all organizations in Italy! The email contained an Ostap Trojan-Downloader disguised as a Microsoft Word document. This down-loader is commonly used as to install TrickBot, a banking trojan that’s steals sensitive information via man-in-the-middle (MitM) attacks, or spreads other types of malware across networks.
Here’s a screenshot from Check Point’s blog post:
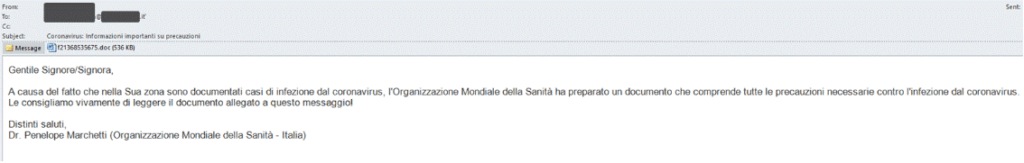
The email translates to read the following in English:
“Due to the number of cases of corona-virus infection that have been documented in your area, the World Health Organization has prepared a document that includes all the necessary precautions against corona-virus infection. We strongly recommend that you read the document attached to this message.
We strongly recommend that you read the document attached to this message.
With best regards,
Dr. Penelope Marchetti (World Health Organization – Italy)”
Although the email didn’t come from an official WHO email address or domain, people who are ignorant of cyber-security threats — or who are caught in a moment of unawareness — could find themselves the victims of a data breach.
Background on the Corona-virus and Why It Makes an Effective Scam Method
Obviously, we’re not global health experts, but here is some basic information about COVID-19:
The Coronavirus Disease 2019 (also known as COVID-19) is something that’s captured the world’s attention — and for good reason. Wordometers.info reports that the virus has infected individuals in 125 countries and territories globally in additional to cruise ships. The Washington Post reports that there have been more than 100,000 cases of the disease reported since late 2019 when the outbreak started, and “several thousand people have died” (although the true number of Corona-virus cases is thought to be “fall above official tally.”)
As the Washington Post reports:
“Corona-viruses range from the common cold virus to more serious diseases that can infect humans and animals, including severe acute respiratory syndrome (SARS) and Middle East respiratory syndrome (MERS).”
But here’s the takeaway we want you to focus on: Even in the grimmest of circumstances, when governments worldwide are trying to slow the spread of the virus among their populations, cyber-criminals aren’t taking a break. In fact, they’re ramping up their efforts, using the global health crisis as an opportunity to steal information from unsuspecting individuals who are trying to stay informed.
To you, hackers, we have one thing to say: You suck. Seriously.
To businesses and organizations, both in the U.S. and abroad, we say the following: Stay informed and keep your employees informed as well.
How to Protect Your Organization from Fake Coronavirus Phishing Sites
For businesses and IT administrators, you know this means that there’s a chance you or some of your organization’s users may find themselves on one of these sites.
What you can do to help prevent users from falling for these phishing scams is:
Keep Employees Informed
Send out information via official channels to keep your employees abreast of the latest Corona-virus news so they don’t go looking for it themselves. Also keep them informed of any Corona-virus-themed threads such as new websites and email scams to look out for.



