Table Of Content:
- 🔴 WordPress site redirects to another site
- 📥What is WordPress Malware Redirect?
- 📥Instances Of Malicious Code in WordPress site
- 📥 How to Detect and Clean WordPress Redirect Hack?
- 📥 How to Prevent future malware redirects
- 📥 WordPress Malware Removal
WordPress website security and protection from malware or malicious code has become more important than ever. Its a well known fact that wordpress is used by more than 40% of websites, due to which it is more prone to hacking attempts than other CMS.
Is your site redirecting to another website?
Then, you are a victim of redirect hack in WordPress. You might be thinking that how do a malware or malicious code make your website redirect.
In this article, we will provide you detailed info about WordPress malware redirect OR url redirect hack fix.
According to Sucuri, WordPress malware infections saw a considerable from 83% to 90% in 2019-20.
We will show you how to fix wordpress site hacked redirecting to another site 🔴 step-by-step. We have also included a video and an infographic (down below) to cleanup malicious redirects in WordPress. You can bookmark for future reference.
It’s important to understand this hack so that you can do a cleanup of your website and also prevent it from reoccurring in future. In case you are short of time, we can remove malware from wordPress site.
Why my website is being redirected to another site?
Often, we come across people asking questions such as why my website is redirecting to another site or to multiple websites. A straight forward answer to website getting redirected is that your WordPress has been hacked and is infected with a malware which sends visitors to a spammy or phishing sites. Know more about WordPress Phishing in this post.
Intent behind inserting such malicious redirects can be black hat seo, or obtaining ad impressions. Attacker exploits vulnerabilities present in your wordpress site via a backdoor or malicious scripts which are hidden in source code. In some case, it also throws a 404 error for your wp-admin area.
This could be due to an infected wordpress plugin, malware injected .header.php and footer.php or .htaccess. We have seen many instances of such hack where WordPress Site URL Redirects to Another Site and have fixed it successfully.
This can negatively impact your business in many ways.
- These hackers may make out money, data and confidential information from your website. If in any case, your website is being redirected to phishing or malware websites then get ready for the consequences.
- SEO loss – Yes, of course, Google is not going to take any chance with its reputation and you are definitely going to be penalized by Google maybe your WordPress site gets blacklisted in google. Google may also show “This Site May Be Hacked” warning message alongside your website listing in search results.
- You host may suspend your website (Siteground suspension). You might get a message like “this site has been suspended” OR Account suspended contact your hosting provider for more information
- Breach of Privacy – It could result in data loss and breach of user privacy, in case, visitors download any software from that infected website unintentionally.
- Branding – A visitor to your hacked site could be redirected to websites selling illegal or spam products which can harm your brand and customers will loose trust in your ecommerce website
- Revenue Loss – If your website uses WordPress woocommerce for selling products, then it can lead to huge revenue loss as well as theft of sensitive information.
What is WordPress Malware Redirect Hack?

“WordPress Malware Redirect” or “WordPress Redirect Hack” is a kind of 🔴 exploit where infected site redirects the visitors to malicious website, phishing page and malware websites. It is likely due to the code injected in your WordPress database, that gets your WordPress site redirected to another site.
Signs & Symptoms – How To Detect
You can easily make out that your wordpress is infected with a redirect malware. Look out for these signs and symptoms to diagnose your site for redirect malware.
- Is your website redirects to another site
- Is your WP-admin shows 404 error while logging in your dashboard
- Are you are unable to access the website dashboard or front end
- Are you unable to log in admin area of your website
- Do you come across this error -““ERROR: There is no user registered with that email address” while loggin in wp-admin.
In case you come across any of the above mentioned symptoms, get in touch with us right away. Our scanner will thoroughly analyze your website, find the location of the hack & start the removal process.
Generally, a malicious WordPress Hacked Redirect is detected through the site’s front end when a visitor is redirected to any other page instead of the page or any website he requested. In most of the cases hackers use a particular malicious code to redirect the website to a porn or scam website to harm your website. Commonly used tricks includes:
- Adding themselves as a ghost admin on your website
- Injecting or uploading a malicious code in your WordPress site
- Executing .php code
If any malicious script is added by hackers it’s often named to look like a legitimate file like that’s the part of WordPress core files on the website. Hackers can add malicious code to wp-content/plugins or wp-content/uploads folders, .htaccess, wp-includes, wp-content/themes, or wp-config.php file.
Examples Of Malicious Codes Inserted in WordPress Sites

Site Redirect Chain – Redirecting from one site to another, automatically
We recently noticed that large number of wordpress sites have been redirecting to malware infected domains such as ibuyiiittraffic[.com] and i.cuttttraffic[.com]. In this kind of redirection malware site webmaster comes across a 404 error on his wp-admin. This is accomplished by infecting the website with backdoor hack or other means of malicious java-scripts being induced by SQL injection or CSS. This is a explicit example of malware redirection ‘chains’ where websites get automatically redirected multiple times before landing on the domain as desired by the attacker.
In other instances, it re-directs when you click anywhere on the page or click ALLOW.

There are many instances found over net while doing a google search where we can see this kind of hack in action. In such cases, we can see that the initially a website redirects to clicks.xxfdftrafficx[.com],then to wwwx.xdsfdstraffic[.com] then to red.goabcdforward[.com], yellowlabel*****.[com] or ticker.*******records[.com] before landing on one of the sites.

We did a google search to find of instances of such redirection hack and got one site which was already infected in SERPS.

There are other instances where, the redirected domain customizes itself according to the location of the user. For example, if a a user is from France or french speaking country, the malware page will translate itself to french language. Same goes for other locations as well.

Other instances of presence of malicious codes, which resulted in random redirection of visitors to malicious sites on hacked WordPress sites decoded.
Javascript redirect
Malicious javascript malicious scripts can also be inserted into widgets by appending Obfuscated javascript to the files.
An attacker can add a few lines of javascript to some or all of the javascript files within the site’s files. A search of site files looking for the URL to which that the site is redirecting might not find any results because this javascript is often obfuscated.
Header.php Injection
In general, the malicious code of 10 to 12 lines is inserted in header.php of the WordPress website.

When this is decoded the main part of the malware looks somewhat like this:

There is a logic behind the code. It will simply redirect the visitors to default7.com if in case it’s the first visit then it can set 896diC9OFnqeAcKGN7fW cookie for 1 year approx. to track the returning visitors.
- Malicious code inserted in footer
- Malicious code inserted in themes header.php file

echo' '; ?>
Depending on the browser and IP a user can be redirected to any random domain listed below
- test0 .com
- distinctfestive .com
- default7 .com
- ableoccassion .com
- test246 .com
- 404.php
Bugs in the Malware
There are various other effects of this malware that are somehow caused by few obvious bugs in the malicious code.
For example, see this line #9 in the decoded version
if ($_GET['6FoNxbvo73BHOjhxokW3'] !== NULL) {
For some reason the malware checks for the 6FoNxbvo73BHOjhxokW3 parameter, generally can’t do anything if a GET requests contains it. It’s not a problem though. The problem is that the code doesn’t make sure such a parameter exists before checking its value. In PHP, this causes a notice like this:
Notice: Undefined index: 6FoNxbvo73BHOjhxokW3 in /home/account/public_html/wp-content/themes/currenttheme/header.php(8) : eval()’d code on line 9
Insertion in htaccess/wp-config.php files
Attacker can do changes in your htaccess file as it is a favorite location for attackers to place malicious redirect [Also Read – WordPress .htaccess hacked]. This file exists on your server and provides directives to server. It sends requests to server which further sends requests to wordpress primary index.php file to be handled. Often, these types of redirect chains (as seen in above examples) will make redirections based on the type of browser or device, or by the site that referred the visitor to your site (most often, from one of the search engines) A htaccess redirect can look like this:
RewriteEngine On RewriteBase / RewriteCond %{HTTP_USER_AGENT} android||meego|iphone|bada|bb\d+\/|blackberry|blazer|compal|elaine|fennec|hiptop|iemobi
RewriteEngine On RewriteCond %{HTTP_USER_AGENT} (google|yahoo|msn|aol|bing) [OR] RewriteCond %{HTTP_REFERER} (google|yahoo|ms
Below you can see an example of hacked htaccess file.

Fake Updates for Internet Explorer Users

The strange case is when you use Internet Explorer the redirect chain may somewhat look like this:
| default7 .com -> advertisementexample .com/d/p/test246.com?k=e88965c228fb1da3ff5ecff0d3034e7a.1462363771.823.1&r= -> maintainpc .soft2update .xyz/vtrescs?tyercv=5qe5FetFrItyco5HNTadzxMu9Nwdv__MlK_dmzyotoo.&subid=102860_bebd063b36f47778fce4592efccae37a&v_id=e5tsIAwpqr6ffJ2kShbqE1F3WXTIU4auGIx7jpVqifk. -> intva31 .saturnlibrary .info/dl-pure/1202331/31254524/?bc=1202331&checksum=31254524&ephemeral=1&filename=adobe_flash_player.exe&cb=-1388370582&hashstring=oZy9K7h7eaHC&usefilename=true&executableroutePath=1202245&stub=true |
This code leads to the websites that push fake java and flash player updates on your screen. see above attached screenshot for reference.

How to detect and fix WordPress Malware Redirect Hack?
Follow these steps to detect and remove malicious redirect hack in WordPress.
- Before you start fixing WordPress malware redirect hack, ensure your website is temporarily put offline. By doing this you can have enough time to solve the problem and also prevent your users from visiting the hacked pages.
- Always backup wordpress database before making any changes in the core files and the database of the website. The backup should also contain the hacked pages and can be be referred in case the necessary content is accidentally removed. Also, be sure to keep a copy of all the files that you work with.
- In case you have less knowledge about JavaScript, CMS or PHP files of your website, it’s strictly recommended to consult a professional to deal with the issue.
What You Can Do To Locate The Hack?
If your WordPress website is infected with site redirecting issue, check the following areas for suspicious links or code:
- Check Core WordPress Files
- Check index.php
- Check index.html
- Check .htaccess file
- Check theme files
- Check header.php (in the themes folder)
- Check footer.php (in the themes folder)
- Check functions.php (in the themes folder)
- Look for adminer script: look for a file named ‘adminer.php’
- Locate this WordPress backdoor
- Check for Fake or hidden admin users: Go to the wp_users table of the database and verify no unknown and unauthorized users are there. [ Also Read: Delete Hidden Admin User In WordPress ]
- Check for both .js and .json files
Follow this simple 5-Step guide to cleanup malware from your WordPress site which results in redirection to another spam site:
 Scanning Your WordPress Site
Scanning Your WordPress Site
There are various ways of checking your site and in any case you find that your website has been hacked with a malicious script, you need to generate a complete backup of your website. While removing malware from wordpress site you might make any mistake and then that backup acts as your savior. Once you have backed up your complete website, you’re ready to run a website scan using our cutting-edge WordPress Malware Scanner.
Additional Tip: You may also try Google Diagnostic Page tool to help you find out exactly which part of your website is infected and number of infected directories/files.
 Find the Malicious Code
Find the Malicious Code
There are number of places where you can locate the malicious code on your website. We understand it’s definitely not an easy task to scan the code chunk by chunk in each page of your website. There are times when the culprit can be enclosed somewhere in your server. And for few places you’ll need ftp/ftps login details to get access to these places to start the malware cleaning process.

- In case, the website is redirecting to an anonymous website(s), then look for the suspicious code in the following areas:
- check both index.php and index.html!
- .htaccess file
- In case your website is triggering visitors for downloads, please have a look at out the following places:
- Header.php
- Footer.php
- Your website’s index file (Check both)
- Your theme’s files
Some of the most sensitive areas prone to infection are index.php, index.html, theme files, etc.
You can also look for malicious code with keywords like ‘eval’ or ‘eval base64_decode’. Apart from this, while performing a WordPress site hacked redirect, an attacker might also inject JS codes in files with .js extension.
PRO TIP: You can also compare the website code from the backup by using various code comparison tools e.g. diff checker or pretty diff to compare your plugin files with the original ones. For this, you have to download the exact same plugins from the WP repository and once installed you can start the code comparison to find out the differences.
If the attacker has access to WP-ADMIN, he can modify the theme files via infected header.php. This can be avoided by adding the following code to wp-config.php file. It will disable the user’s ability to change PHP files via wp-admin.
define( ‘DISALLOW_FILE_EDIT’, true );
Let us handle all the time consuming work, our WordPress security experts can take care of entire process. Contact us here.
 Deeper Dig in the website
Deeper Dig in the website
At times there is no harm in running tests to analyze whether your website is infected with a malware/malicious code or not. For this, you can use any test to pretend you’re a user agent or Google bot using a googlebot simulator or you can also use FETCH AS GOOGLE from the website’s webmaster console. There are few commands that work through ssh client. By employing certain code you can look into that place where the hacking has been done and further WordPress malware removal can be done manually too. [📒 Also Read – How to Scan & Detect Malware in WordPress Themes ]


 Removing Bad Code / Pages From Google
Removing Bad Code / Pages From Google
Firstly, You’ll need to remove the malicious scripts that causes website redirection to the abusive sites. Identify all the pages on your website with malicious code and remove them from search engine. These website pages can be removed from the Search Engine Results together by using the remove URLs feature and by going to Google Search Engine Console. Also, update the plugins, themes and ensure the new core theme is installed plus up-to-date. Change or reset the passwords, Regenerate WordPress Salt Keys using this tool.
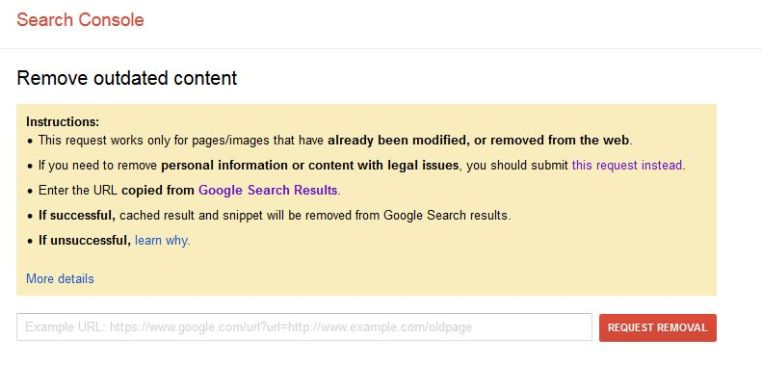
 Submit Malware reconsideration request using Search console
Submit Malware reconsideration request using Search console
Google Webmaster tool is one of the best tool for webmaster which you can get for free, and if you have not yet submitted your Website in GWT, you are missing out many vital information regarding your website. Here I’m sharing step by step guide to put malware review request using Google Webmaster tool:
- Login to Google search console
- Verify your Website ownership
- Click on Site > Dashboard > Security issue
Here you will see list of URL, google is suspecting that is infected with malware. Once you have cleaned all hacked files and your website is malware free, simply click on request a review, and add notes in the form of actions you have taken to remove the malware.







